=
In 2026, cyber threats are surging. Discover practical tips for securing your data against hackers.
Cyber Attacks: A 2026 Reality Check
Here’s a no-nonsense fact for you: In 2026, cyber threats aren’t just rising—they’re exploding. You’ve got more hackers out there than ever, and they’re armed to the teeth with tools that’d make a top-tier spy sweat bullets. Just last year, 75% of businesses reported at least one breach, and we’re talking breaches that cost companies millions, not a couple of bucks.
If you’re sitting there thinking your company’s immune just because you’ve got a firewalled fortress, think again. Hackers today have found ways to bypass security systems faster than most factories ship a mouse pad. And let’s not even start with those so-called “smart” locks that, in reality, are just one firmware bug away from being a hacker’s dream come true. Installing a smart lock without layered security—priceless mistake. The statistics show that smart locks require up to thrice the security layers compared to your grandpa’s old padlock.
Smart Locks vs. Traditional Padlocks
Look, everyone loves to jump on the smart lock bandwagon. Install an app, control access remotely, voila! Instant security, right? Wrong. According to recent findings, over 40% of smart locks fail basic security audits. The issue isn’t just with vulnerabilities—though there are plenty—but with overconfidence. People are lulled into a false sense of security.
Take those Wi-Fi-enabled locks, for example. They’re nifty until your neighbor’s kid accidentally hacks into it with a toy drone controller. I’ve seen it happen. Traditional padlocks, however? Less flashy, but they’ve got 150 years of reliability behind them. A solid hardened steel shackle might not send you notifications, but it won’t abandon you when the battery dies.
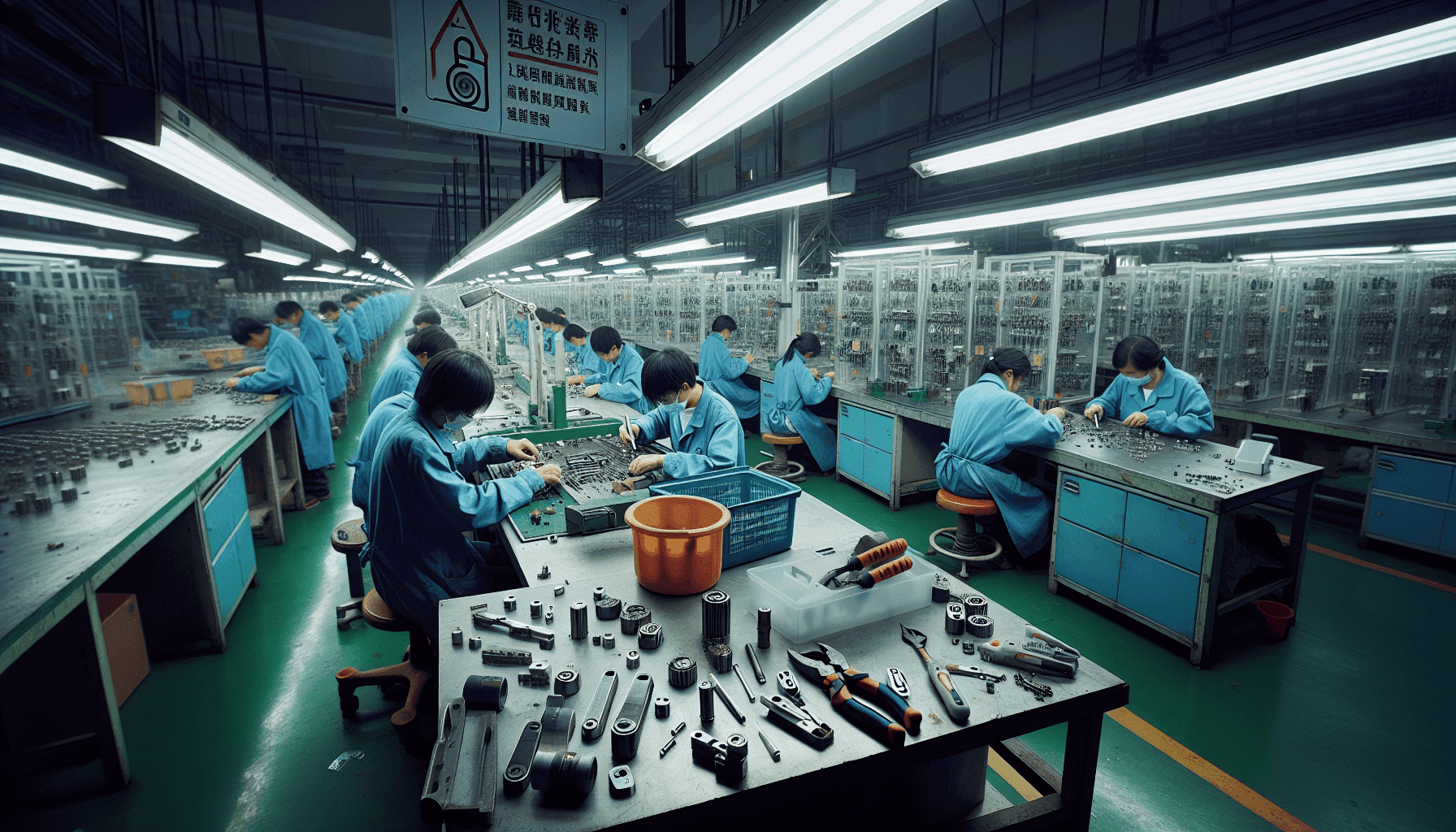
Plus, we’ve all seen how most manufacturers approach the “CE certified” claim. Most vendors slap a label on and call it a day. But then, under the microscope, those locks crumble like cookies in a salt spray test. That’s why at Yuefong Lock, we don’t just talk about CE standards; we torture-test every batch for 120-hour salt spray endurance. Why? Because we’ve owned the mold shop since ’82—it matters that much.
Navigating IoT Vulnerabilities
IoT devices, including smart locks, listen more than they should. And not just to the good guys. MIT researchers found that over 60% of IoT devices have exploitable software flaws. This isn’t about scaremongering—it’s about reality. Patch updates, encryption, and secure firmware development—words tossed around like festive confetti yet rarely implemented with sincerity.
You’re either in the 20% investing in serious, ongoing security improvements, or the 80% hoping for the best. Spoiler: hope isn’t a strategy. Companies that think a single patch job will fix their smart lock security are living in a fantasy. Only certified updates and consistent monitoring shield you from the usual network traffic buggery and authentication lapses.
The Overlooked Art of Physical Security
Everyone talks digital and forgets the physical aspect like it doesn’t exist. When was the last time your security plan included physical access audits? Experts say that physical breaches often enable hackers to swipe data before virtual defenses even light up. Let’s not forget—40% of all cyber-attacks start offline, with a simple break-in.
This is why mixing layers (physical and cyber) is not just recommended—it’s essential. Looking back at those rigid combo lock designs from decades ago, we see a simplicity so secure, it’s humorous. Yet, few companies bother with practical, tried-and-true security methods in the midst of whiz-bang technological advancements.
Securing Communications Channels
And there’s another Achilles’ heel: neglected communications channels. Believe it or not, unsecured comms lines can render that fancy security hardware almost useless. A study in 2025 showed that 70% of security breaches involved compromised communications. Encryption may sound basic, but it’s still violated more often than we admit.
Look at something like TLS (Transport Layer Security) for example. It’s evolved, sure, but many are still using outdated versions or, worse, skipping them altogether. Bad habit. Every factory and business must ensure they are running the latest encryption protocols—because it takes minutes to breach an unprotected channel.
The Human Element: Biggest Hole in the New Firewall
Then there’s us–humans. Our habits are our worst enemy. 85% of cyber incidents in 2025 came down to human error. Phishing, lousy password hygiene, you name it. You can install the priciest lock, but if the code scribbled on a sticky note makes its way online, game over.
Security training, then? Not just once a quarter. It needs repetition and evolution alongside threats. Train your team rigorously, simulate attacks regularly, and remind them that their actions are every bit as crucial as credentials on a firewall. Draconian? Maybe, but quite indispensable when we’re dealing with billion-dollar liabilities.
Consider that while automation keeps evolving, humans are still integral to operations. Those saving grace moments are when a vigilant employee notices a breach and acts swiftly before the trap closes. Automated responses will follow eventually, but initial warning comes from familiar eyes.
Next Steps: Making Security Hardware Work for You
So, here’s where you might actually get some sleep at night. First, embrace a hybrid security model—mix the old with the new. Pair smart locks with traditional hardware security. Integrate network monitoring tools with physical security measures.
- Regularly audit and update all systems, both digital and physical.
- Encrypt communications properly and verify all connected devices’ integrity regularly.
- Train staff often, enforcing safe practices without compromise.
Finally, hold manufacturers to higher standards. Only demanding customers ensure development in security tech that actually works. And remember—a shackle isn’t just metal, and a smart lock isn’t just firmware. They’re your peace of mind.